After being in preview for quite some time, Azure Storage Explorer is now available in general availability (GA).
You can get it from:
- For Windows https://go.microsoft.com/fwlink/?LinkId=708343&clcid=0x409
- For MacOs https://go.microsoft.com/fwlink/?LinkId=708342&clcid=0x409
- For Linux https://go.microsoft.com/fwlink/?LinkId=722418&clcid=0x409
With Azure Storage Explorer you can directly access your Azure Storage from your preferred client to download/upload content, manage you blobs, files, queues, tables or even your Cosmos DB Entities.
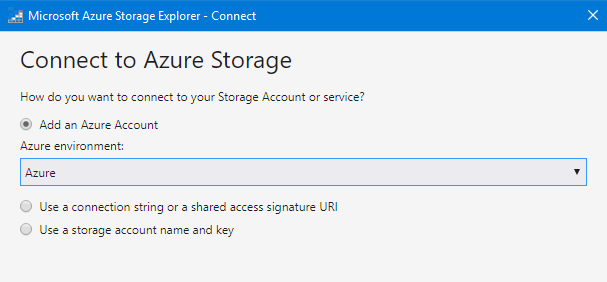
To connect to your Azure tenant (covering all public, government or China) you can use either your credentials, a connection string or shared access URL or the storage account key.
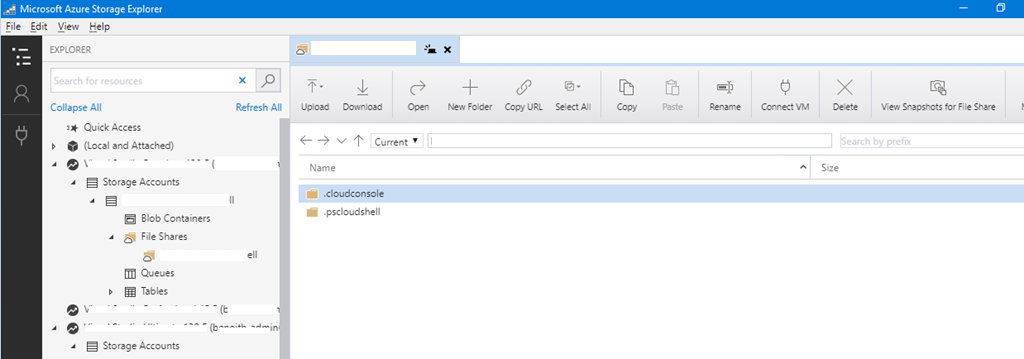
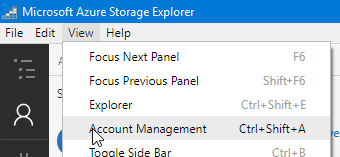
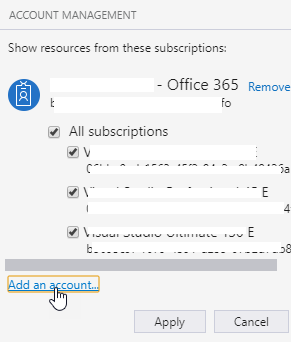
You can add multiple accounts to connect to your Azure Storage using the View\Account Management menu.
Azure Storage Explorer in the web portal – Preview
After releasing the GA version of the Azure Storage Explorer tool (see https://t.co/pb8nRwDRqi) Microsoft is making the Storage Explore available through the Azure portal.
To enjoy this new capability, just logon to your Azure portal and access the Storage account you want to explore and reach the Storage Explorer blade
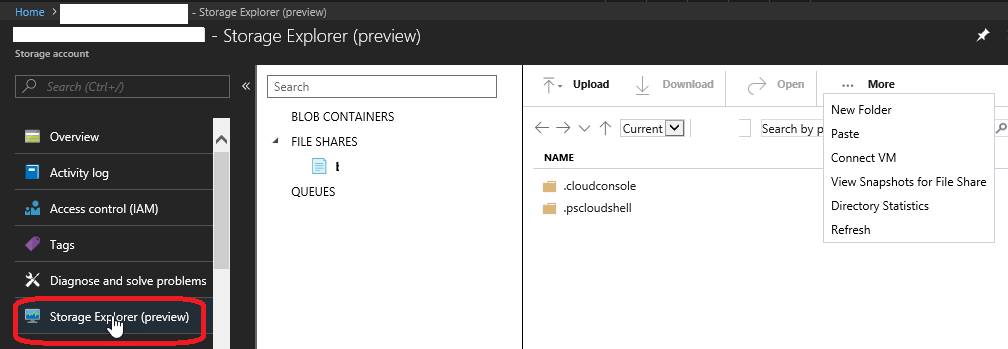
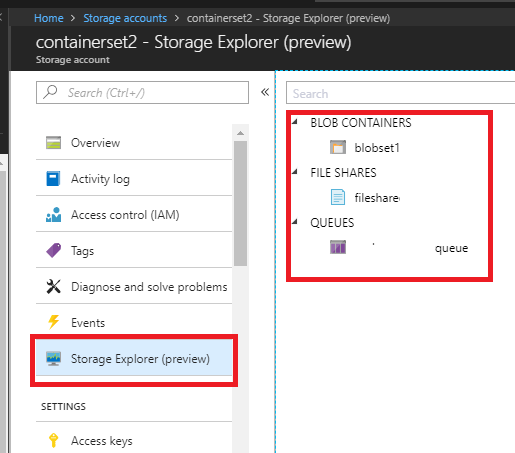
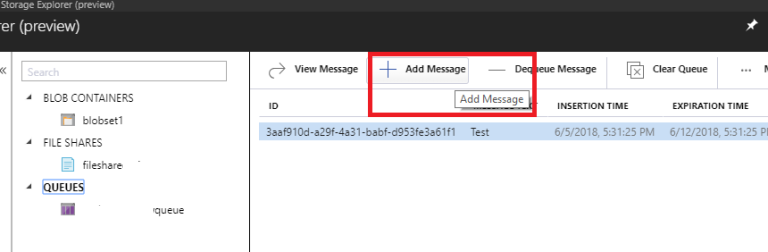
From here we have options to manage,create Blob Containers, File shares and queues
New Blob Containers can be created deleted managed
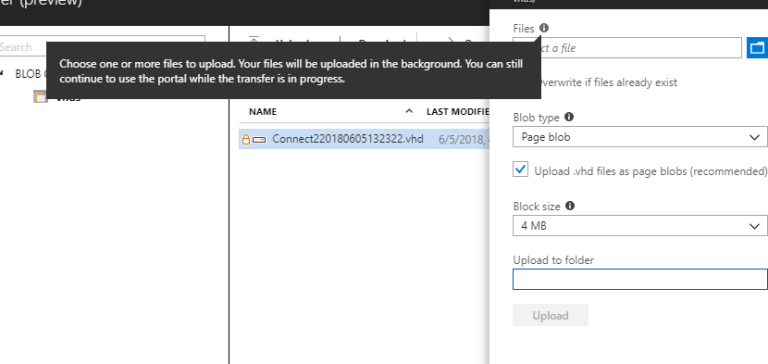
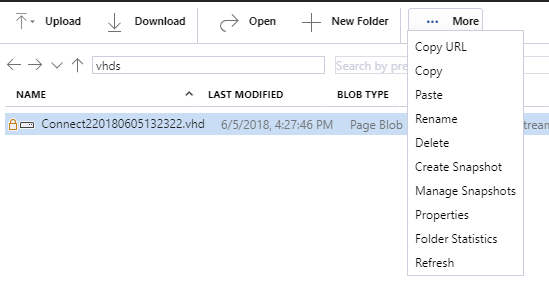
we can further drill down and manage properties
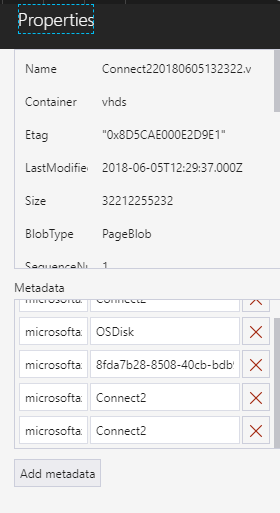
These are the options variable in the properties
Same way the file-share can be created deleted and managed
Also we have an option to upload files, connect to VM and download from here.
Azure AD Authentication – Grant Access to Azure Storage
As you know Azure Storage is providing storage capabilities on Azure (either for files, blobs, queues or tables).
Until then, when you needed to grant access to a storage space on Azure you had to use shared keys or SAS tokens.
Now you can also use your Azure AD to grant access to Azure storage, making things simpler when you have to provide access to your organization users using the Role Based Access Control capability.
As the service is currently in preview, the capability is limited to Azure Storage Blob and Queue Service.
To start using the feature, you can either use Azure ARM portal, Azure PowerShell, Azure Cli or Azure Authorization Resource Provider API.
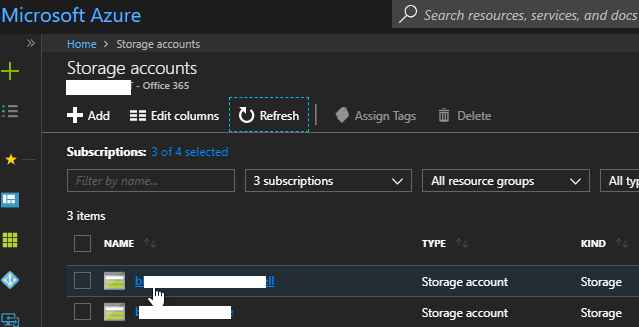
- Logon to your Azure portal (https://portal.azure.com/) and access your storage account
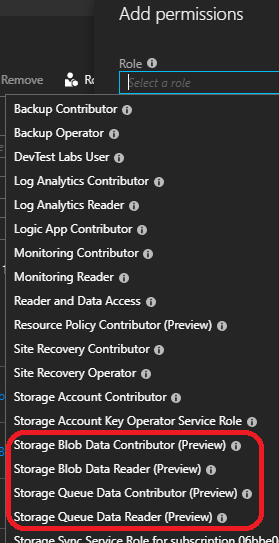
Then access the Access control (IAM) blade and Add a permission
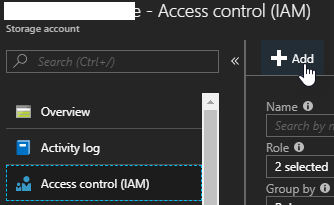
Grant the permission – either Storage Blob Data Contributor (Preview), Storage Blob Data Reader (Preview), Storage Queue Data Contributor (Preview) or Storage Queue Data Reader (Preview)
If you want to use Azure PowerShell or Azure Cli, see the documentation here https://docs.microsoft.com/en-us/azure/storage/common/storage-auth-aad-script
Hello Hammad! This type of Azure Storage content creates new hope and inspiration within me. I had a chance to get some useful and unique information. Thanks for sharing an article like this.